Tool Release: UAL-Timeline-Builder (UTB)
Link to UAL-Timeline-Builder: https://ual-timeline-builder.sagalabs.dk
Link to Github: https://github.com/SagaLabs/UAL-Timeline-Builder
Ever wondered how to approach a new Business Email Compromise (BEC) case?
You know that the customer is using M365 and you have exported the Unified Audit Log, but overwhelmed by the amount of data. 😮💨
Sagalabs is proud to announce that Christian, our scenario lab designer has just released a new utility for your incident response tool belt. The UAL-Timeline-Builder. 🕵️♂️
Why might you need this tool?
The tool intends to help you in your M365 BEC investigations or prepare the UAL for import to SIEMs. 📊
The tool features simple but effective filter functionality to make the data more readable. A lot of times the investigations in BEC take a lot of time to acquire & prepare data before it can be analyzed effectively in BEC-type cases. This tool will help you to do it.
It also includes the raw data event for you to validate. It also has a simple search function that takes keyword searches, for example, you can search the MailItemsAccess for a subject keyword.
The tool is not specifically designed for huge datasets, however, it has been tested on quite large environments and runs well.
Features
✅ Import standard CSV based Unified audit log.
✅Option to filter on risky operations, making it easier for you to find those nasty new Mailbox-rules.
💾 All data is processed with the help of in-browser local storage so that means that no data is sent to a server or stored in a database anywhere. We are using Azure Static Web Apps to do this.
💾 Features an export function to make the data available in ndjson, suitable for import directly into SOF-ELK or similar.
How to use the tool
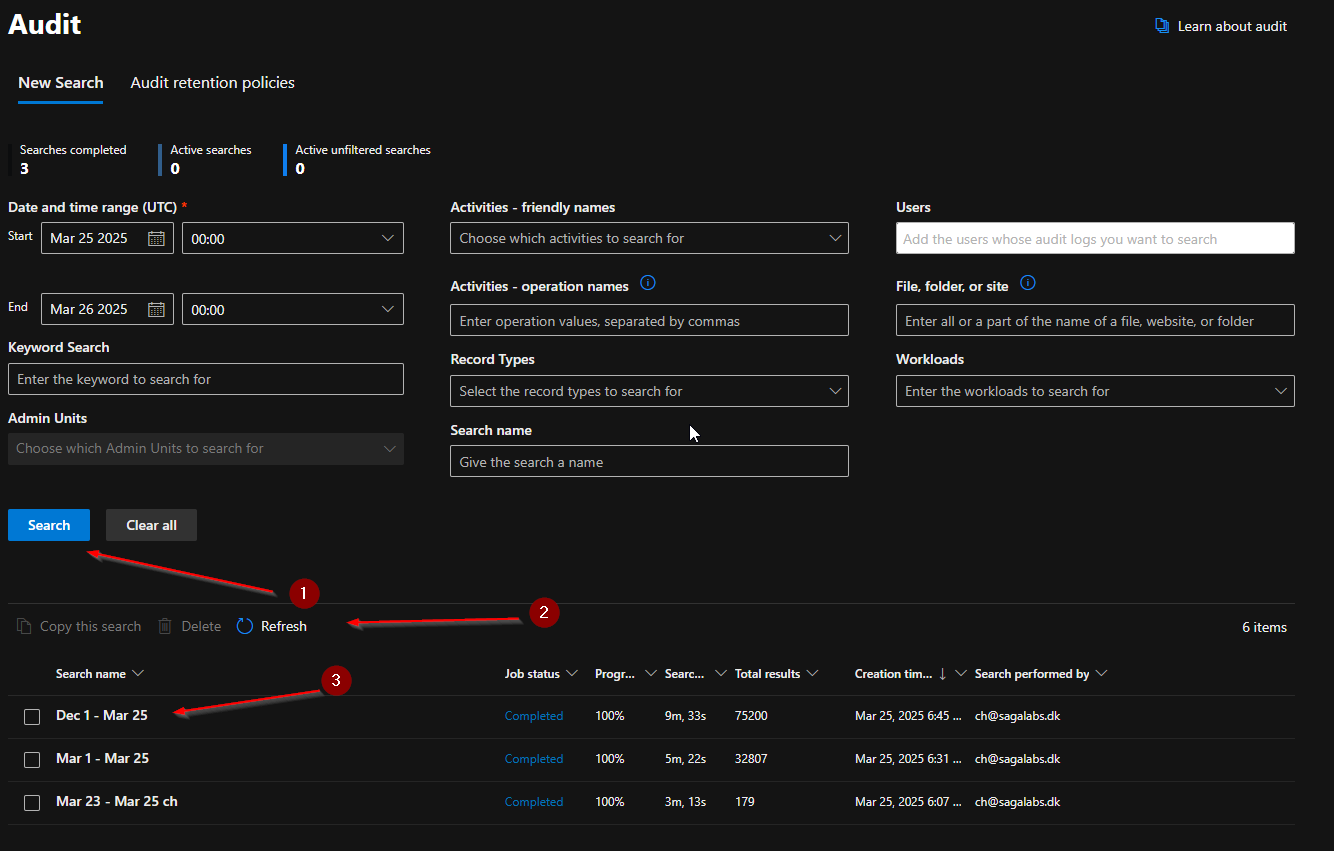
For the utility to work we need to export the unified audit log as a CSV.
The unified audit log can be found on: https://security.microsoft.com/auditlogsearch ℹ️ It requires AuditLogsQuery.Read.All permission to do that.
First to go the Unified audit log
Define what your export should include. Some like to export the whole UAL (me) or some target specific compromised users.
Note that depending on the size of the environment, this search can take a long time.
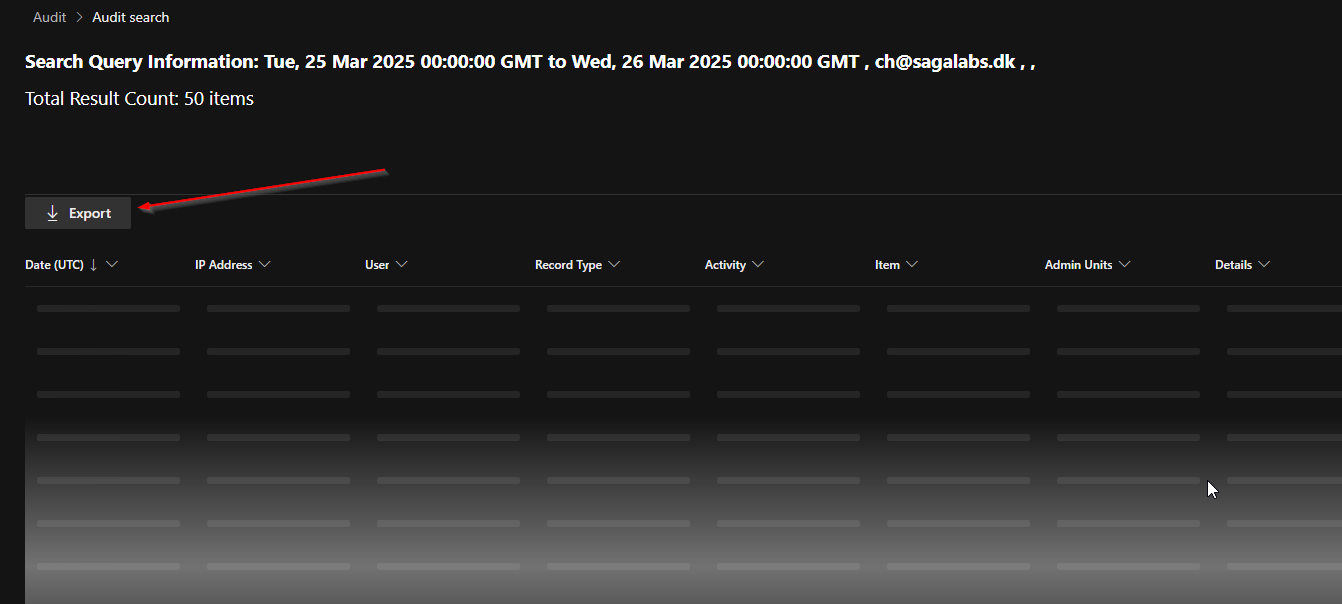
Now click Export
This can take a long time (depending on your search criteria) because this is where Microsoft is converting stuff into a CSV for you.
Once the export is finished, download it
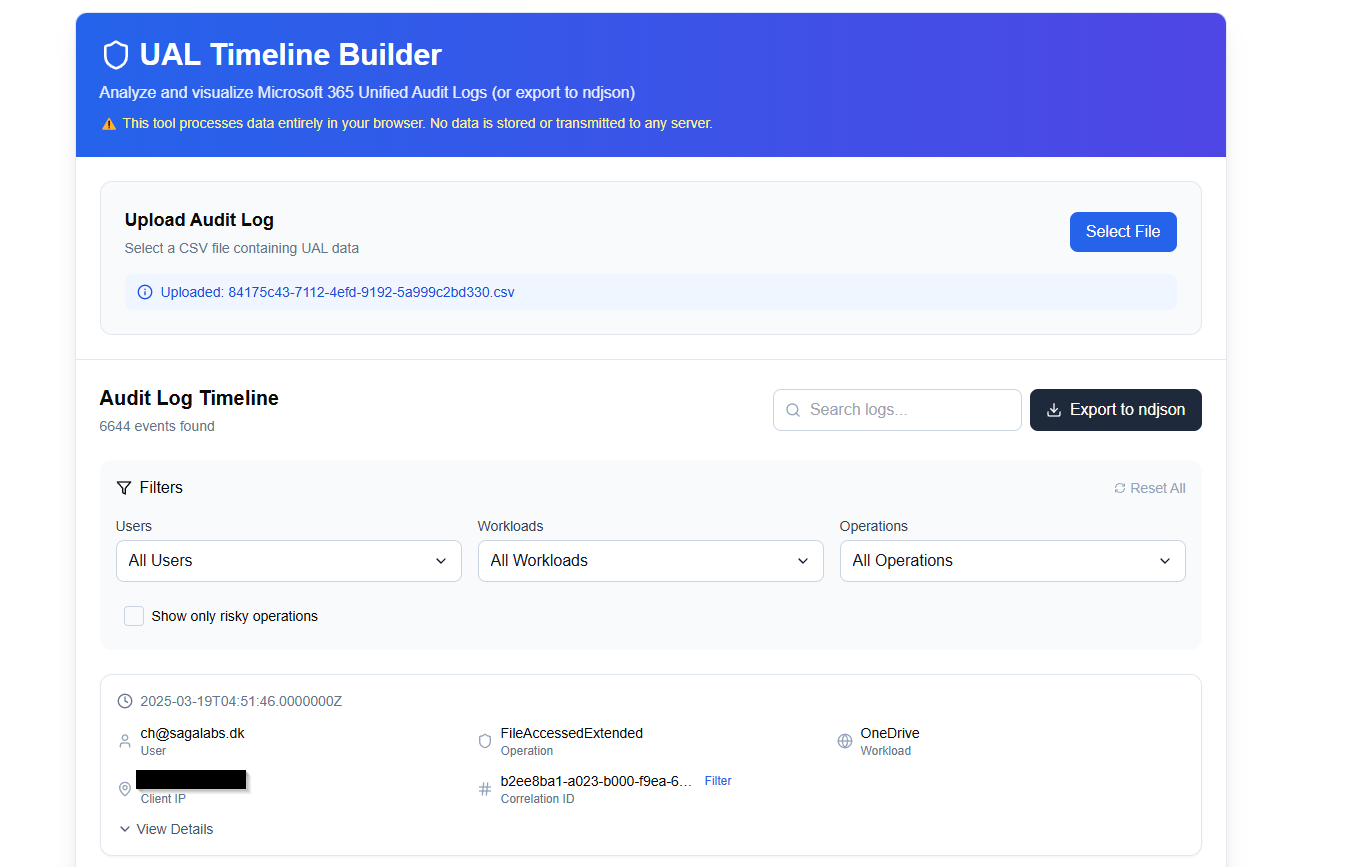
Next step is to import the CSV into UTB, and let it do it’s magic. 🔮
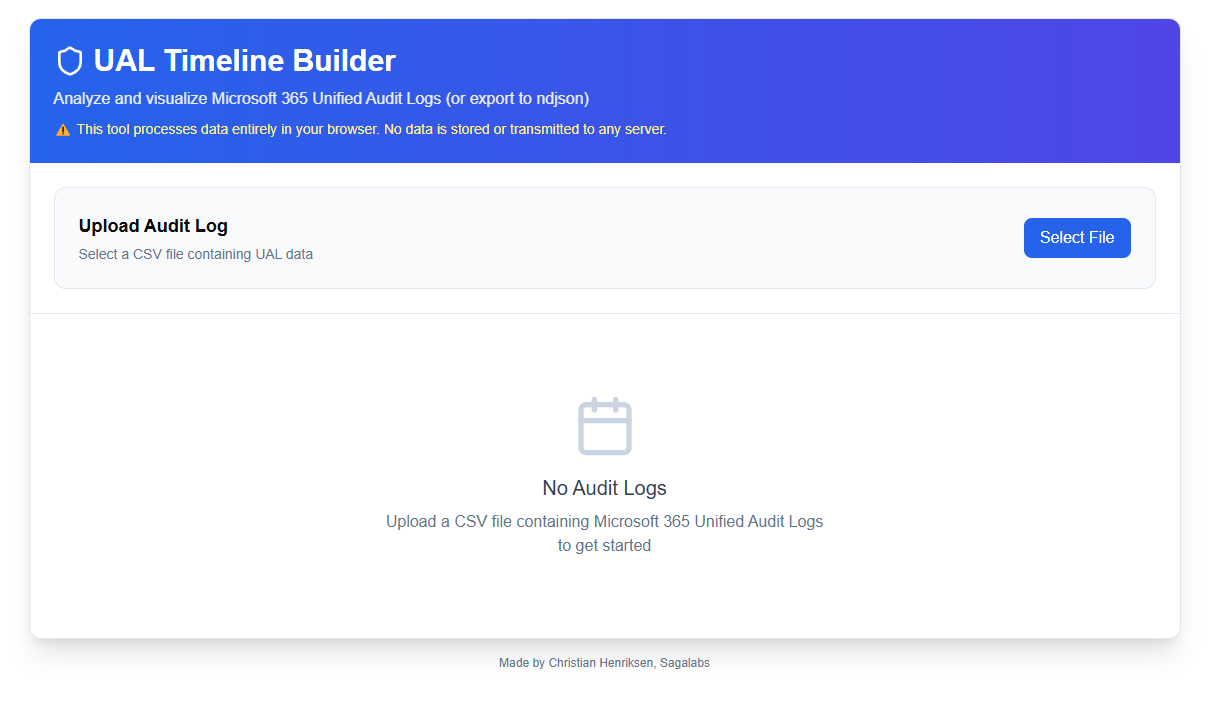
Go to: https://ual-timeline-builder.sagalabs.dk to access the tool, yup totally free. 💸
After importing the data, you should see a list of the entries. The entries are sampled to only show the 100 first entries to increase performance. Note that all processing is done in the browser, so nothing is sent anywhere.
Filters
UTB supports 5 types of filters currently:
User
Workloads
Operations
Risky operations (defined in the tool)
Search
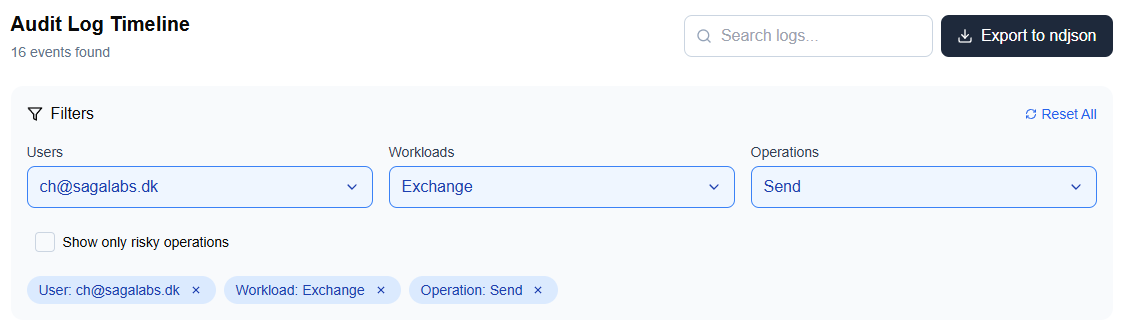
For example, let’s take a look at all the risky operations on [email protected].
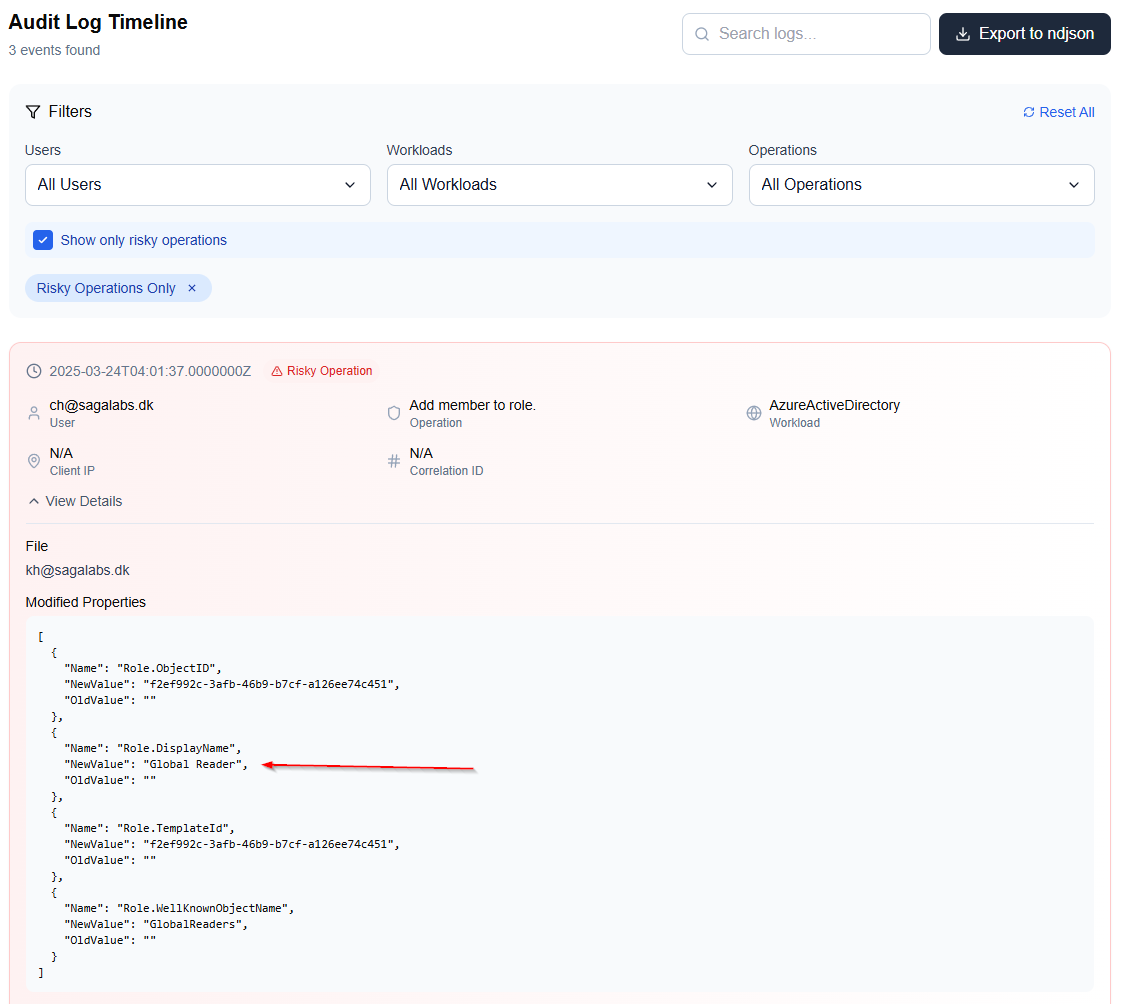
For example we can see that [email protected] added [email protected] to Global Reader on 2025-03-24.
For simplicity and awareness, the tool marks the risky entries as read for you to easier find them.
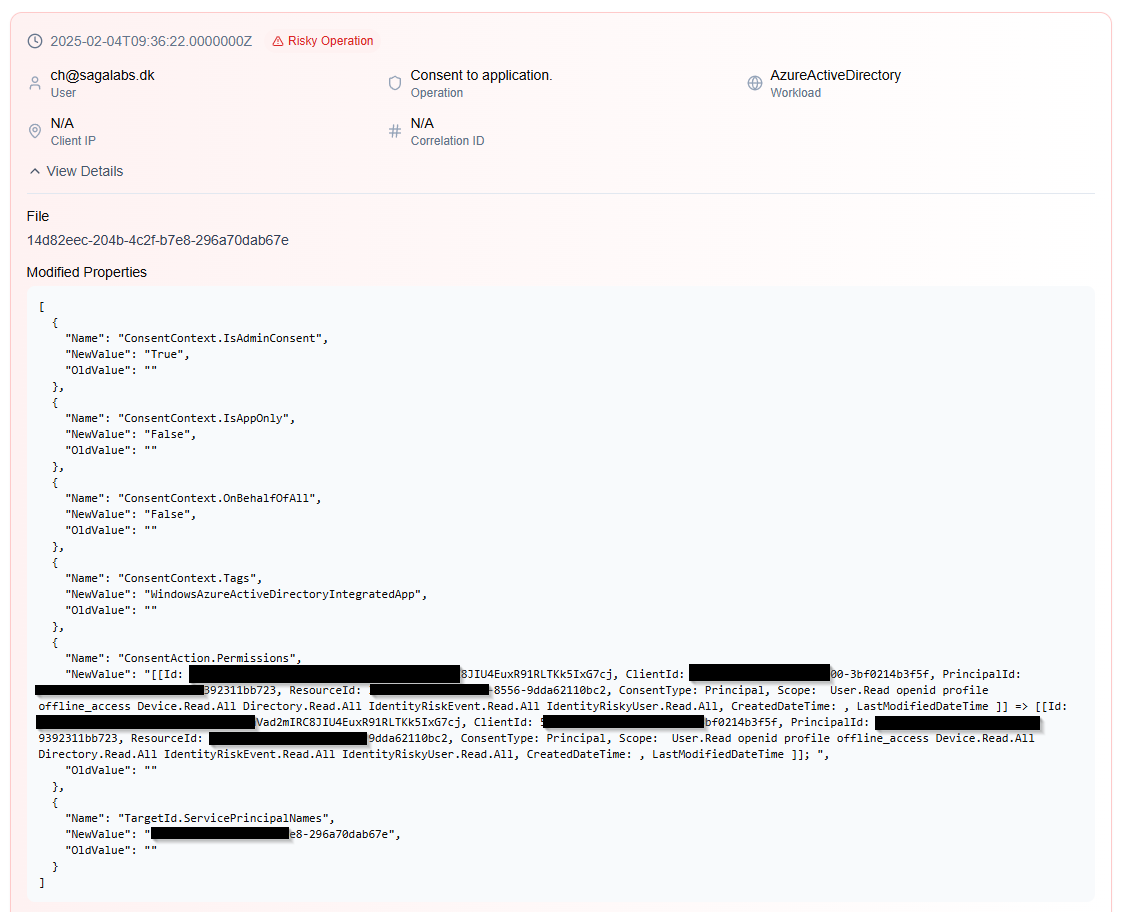
We can also see that the malicious user also contented to an application:
Export & Import to SOF-ELK
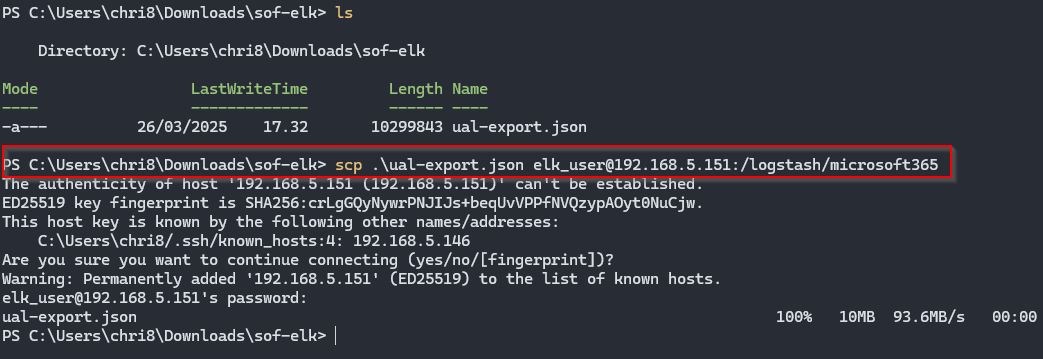
To export to JSON format, simply just click the “Export to ndjson” to get the .json file.
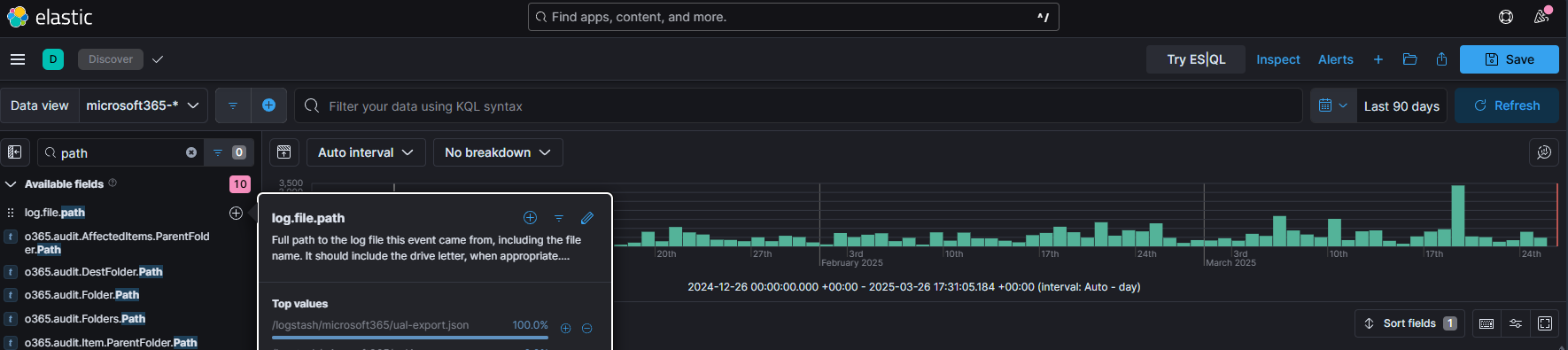
Now lets it into your SOF-ELK instance
I like to use SCP to transfer it to the SOF-ELK host
Remember to place it in the /logstash/microsoft365 dropdir for the logstash pipeline to pick it up. 🎉
Wrapping up
We hope you will find a good use for this small nifty utility. The tool has been heavily inspired by a chat I had with Korstiaan Stam from https://www.invictus-ir.com during some Cloud training - thanks!
If you have any ideas for features, please reach out. Below you can find a list of the features that I’m planning to implement in the near future.
Feature Roadmap:
Statistics function to output all IPs that have logged in, including GEOIP mapping making it easier for you to locate suspicious activity.
User-agent analyzer
Make it able to analyze Azure tenant logs
Open-source the whole project
Export to other SIEMs
Make the search functionality stronger with conditions
Message ids
✨ Dark mode (🔥PRIO 1)
Better display for inbox rule
Click an event to add to a timeline